What is a cyber tabletop exercise?
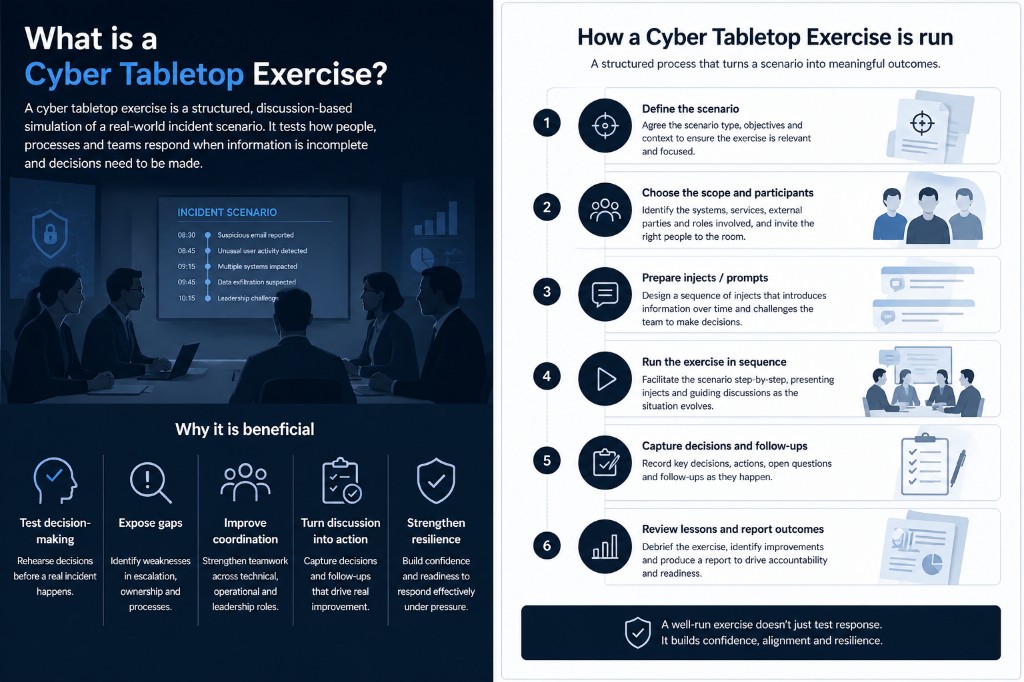
A cyber tabletop exercise is a structured, discussion-based simulation of an incident scenario. It is designed to help organisations work through how they would respond if a realistic cyber event were to unfold, without affecting live production systems or waiting for a real incident to force those decisions in real time.
Rather than focusing on technical exploitation or running active attack tools, a tabletop exercise focuses on people, process, judgement, and coordination. The aim is to test how an organisation has defined its governance to help individuals and teams interpret the situation, escalate issues, classify the event, and work together when the available information is incomplete or evolving.
These exercises are usually delivered through staged prompts, often called injects. Each inject introduces new information into the room, such as a user report, a suspicious login, an internal email, a supplier notification, a monitoring alert, or a challenge from leadership. This allows the scenario to unfold in sequence, giving the team realistic points at which to assess impact, make decisions, and determine what should happen next.
A good cyber tabletop exercise does not try to “attack” the organisation. Instead, it tests how prepared the organisation is to think, communicate, escalate, and act. It gives technical teams, operational teams, managers, and leadership a chance to rehearse together, understand their roles, and identify where assumptions or gaps may exist before a real event occurs.
In practice, that means a cyber tabletop exercise is often as much about governance, ownership, decision-making, and communication as it is about security tooling. It can reveal where escalation paths are unclear, where teams do not share the same view of severity, or where business and technical priorities become misaligned under pressure.
Why is it beneficial?
One of the biggest benefits of a cyber tabletop exercise is that it gives teams the opportunity to rehearse decisions before they have to make them under real pressure. It is far easier to identify gaps, confusion, and weaknesses in a structured exercise than during a live incident, when time, impact, and reputation are already on the line.
A tabletop exercise helps organisations test how decisions are made when the picture is incomplete. In many incidents, teams are forced to respond before they have perfect information. They may not know the full scope, the exact cause, or the total impact. A good exercise helps people understand what level of uncertainty is acceptable, when to escalate, and how to balance caution with action.
It is also valuable because it exposes gaps in ownership and escalation. On paper, many organisations believe they know who should lead, who should be informed, and when a technical problem becomes a broader organisational issue. In a tabletop setting, those assumptions are tested. It becomes much easier to see whether responsibilities are clear, whether teams agree on severity, and whether the right people are brought in at the right time.
Another major benefit is cross-functional coordination. A cyber incident rarely belongs to only one team. Technical teams may investigate the signal, but legal, communications, operations, leadership, and third parties may all need to be involved, depending on the nature of the event. A tabletop exercise helps these groups understand how they work together, what they need from each other, and where handovers may be weak or unclear.
Ultimately, the value is not only in running the session. The value lies in helping the organisation become more prepared, more aligned, and more realistic about how it would actually behave during an incident. That is what makes tabletop exercises an important part of resilience rather than just a workshop activity.
How is it typically run?
A cyber tabletop exercise usually begins with defining the scenario. This means deciding what type of incident the exercise is trying to simulate, what the organisation wants to test, and what context needs to be established before the session starts. The scenario might involve data exposure, unauthorised access, ransomware, third-party compromise, shadow IT, insider actions, or a public disclosure event. The goal at this stage is to make the scenario relevant enough to generate meaningful discussion.
Once the scenario is defined, the exercise scope is set. This includes identifying which systems, services, business areas, external parties, suppliers, and teams are relevant to the exercise. In some cases, the exercise may focus on internal infrastructure and operational systems. In others, it may include external services or unmanaged platforms that are central to the scenario, even if they do not exist in the organisation’s approved inventory.
Participants are then selected. This often includes a facilitator, core operational or security responders, and potentially leadership, legal, communications, or business stakeholders, depending on the scenario. A good exercise should make it clear who is expected in the room and why, because that shapes the quality of the discussion and the decisions made.
The scenario is then broken into injects or staged prompts. Rather than presenting the entire incident upfront, the facilitator introduces information in sequence. This might begin with room narrative and background context, then move into a technical signal, followed by external confirmation, escalation pressure, or executive challenge. This staged approach allows the room to experience the incident as it would likely unfold in reality, where information arrives in waves and certainty develops over time.
During the exercise itself, the facilitator moves the team through the scenario one step at a time. The role of the facilitator is not only to read out prompts, but also to manage pace, keep the discussion focused, and ensure the conversation stays aligned with the objectives of the exercise. Teams discuss what they would do, what assumptions they are making, what they need to confirm, who needs to be involved, and what immediate decisions should be taken.
As the exercise progresses, it is important to capture what happens in the room. That includes key decisions, actions, follow-ups, open questions, and any issues that clearly require improvement after the exercise. Without this, the organisation may gain the benefit of a good discussion but lose the practical outcomes once the session ends.
The final step is review and close-out. This is where the organisation reflects on what worked, what caused confusion, what gaps were exposed, and what actions should be taken next. In a stronger exercise process, this review becomes a structured record rather than a loose memory of the meeting. That allows the exercise to support reporting, accountability, and improvement work after the event.
How CloudPilot supports this
CloudPilot supports this workflow by turning the exercise into a structured operational process rather than a collection of slides, facilitator notes, and disconnected action lists. It gives teams a way to plan, run, review, and report on cyber exercises within the same platform, with clearer continuity from scenario setup through to follow-up.
At the planning stage, CloudPilot helps define the exercise itself. Teams can set the title, scenario type, facilitator, and scope, and identify the systems, servers, and external parties that matter to the scenario. This creates a more grounded starting point than a generic exercise document, because the scenario is tied to the operational and resilience context the organisation is actually concerned with.
CloudPilot also helps structure the scenario through ordered injects. Instead of relying on a static agenda or unstructured notes, the exercise can be built as a sequence of scenes or prompts that unfold deliberately. Facilitators can prepare room narrative, alerts, emails, chat-style events, or other inject content in advance, shaping the exercise as a guided experience rather than an improvised discussion.
Another important part of the workflow is role alignment. CloudPilot allows exercises to be tied to an organisation’s broader response role model, helping define which roles are in scope and who is expected to respond at each stage of the scenario. This makes the exercise more operationally useful because it clarifies not just what is happening, but who should be involved and when.
During the run itself, CloudPilot provides a facilitator-led view of the exercise. The scenario can be advanced in sequence, helping the room move through the injects in a controlled way rather than jumping around or losing track of the narrative. This gives the exercise more pacing and structure and makes it easier to keep attention on the current decision point.
As the room responds, CloudPilot allows key decisions and follow-up actions to be captured directly against the exercise. This is one of the biggest improvements over a traditional tabletop exercise run through slides or notes. Important outcomes are not left in someone’s notebook or spread across multiple tools. Instead, they remain tied to the scenario and available for review afterwards.
At close-out, CloudPilot supports structured review and reporting. Teams can record lessons learned, follow-up actions, and final observations, then generate a report that reflects the same scope, injects, decisions, and actions captured during the session. This gives the organisation a more useful record for leadership, audit, resilience review, and improvement planning.
In that sense, CloudPilot does not replace the judgement, discussion, or facilitation that makes a tabletop exercise valuable. What it does is give those activities clearer structure, stronger traceability, and a better path from exercise discussion to practical follow-through.